While it’s been almost 15 years since the concept of “bring your own device” (BYOD) was first discussed, its popularity has had its fits and starts.
But with the pandemic-driven shift to remote and hybrid models, BYOD has found its stride, enabled by changes in workplace models, enhanced capabilities to monitor and manage devices, and more sophisticated cybersecurity solutions.
To that extent, 69% of business leaders in the US feel positively about the role BYOD plays in the modern workplace. However, despite the ability to fence and secure mobile devices, BYOD does continue to carry some increased levels of risk.
When you add confidential intellectual property, compliance, and sensitive customer data to the mix, BYOD security risks become clear. However, BYOD risks don’t have to limit its usage. Rather, the right security measures can empower organizations to take full advantage of the flexibility of BYOD.
Even with bring your own device to work security issues, most companies find the pros of BYOD – familiarity, flexibility, and productivity, just to name a few – significantly outstrip the problems with BYOD when managed appropriately.
In this article, we’ll take a look at some common examples of BYOD security risks, and what you can do to avoid them to prevent data loss while improving device security.
Steer Clear of BYOD Risks and Issues With ExigentWork with our security experts and mitigate the many risks of BYOD. |
Over the years, technology has greatly improved when it comes to monitoring, managing, and securing personal devices being used for business.
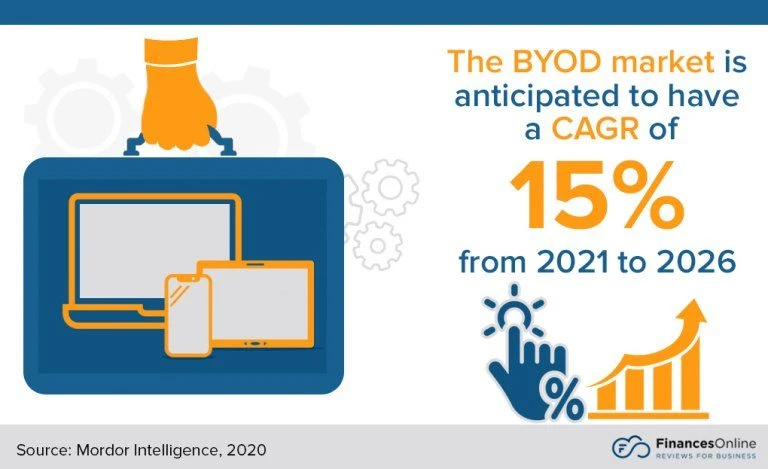
As a result, it’s easy to see why the BYOD market is primed to have a compound annual growth rate (CAGR) of 15% between 2021 and 2026, and that 80% of US companies have used BYOD since 2018.
Despite that, the security risks of BYOD remain, especially with today’s highly sophisticated cyber threat landscape. Outside of security, there are other challenges with BYOD, including compatibility issues and data protection, backup, and retrieval.
There are also ongoing challenges regarding the ownership of data when it comes to remotely wiping data files, how to manage a mix of personal data and company data, and what to do when there is a lost or stolen device.
Before an organization determines whether to allow employees to bring their own devices to work, there should be a thoughtful and thorough analysis of the management and security investments that will be required, along with a strategy for creating detailed policies, before a successful BYOD rollout can happen.
To consider:
Nearly all BYOD risks are tied to the corporate data that lives on BYOD devices, everything from intellectual property to customer data to payment information.
Monitoring the flow of data and securing it at every single point of access can be a huge challenge that adds to BYOD risks.
Scenarios range from phishing attacks to using public Wi-Fi in a coffee shop or hotel lobby to systematic hacks that leverage an employee’s device as a doorway to a larger company network and all its sensitive data.
The most common BYOD security risks include:
Adding to BYOD risks and issues are insufficient policies and compliance regulations, which can increase confusion on both the management and device usage sides.
As employees’ technology expectations continue to grow, the user experience must also be considered. Cybersecurity solutions that slow productivity and create frustrated users are rarely effective.
As mentioned before, while BYOD security risks have grown with its popularity, so have the sophistication of management tools that support increased usage of personal devices.
An increasing number of hybrid workplace solutions are available, priced, and configured for businesses ranging from small to enterprise-class.
These solutions often address access and security issues by enabling easy device tracking and management, offering sophisticated locking and data wipe capabilities, and making the application of network-wide, advanced cybersecurity policies simple and easy.
Additionally, virtual and hybrid workplace environments are much more easily configured so that personal data and sensitive or confidential corporate information are clearly partitioned, making it easier to control access, limit malicious activity and wipe only authorized information in case of a stolen or compromised device.
Despite the widespread availability of superior technology solutions to support BYOD, any organization exploring BYOD as a permanent option for their employees should partner with an experienced managed IT services provider.
This will not only help you plan the software needed to support a BYOD initiative but also to provide expert monitoring and management services alongside BYOD-specific security policies and measures.
Interested in learning more about how to avoid BYOD risks and issues? Check out these blogs: |
At Exigent Technologies, our team has been both using and supporting personal devices in the workplace for nearly 20 years. This makes us uniquely qualified to resolve the common problems with BYOD.
Additionally, with our extensive compliance and cybersecurity practices, Exigent can offer detailed guidance on BYOD security measures, including policy creation.
For more information about how we can help you mitigate the many bring your own device to work security issues, contact us today to schedule a free consultation with our team.
Daniel Haurey Jr. is the president and founder of managed IT services provider Exigent Technologies, which he founded in 1997. Under his leadership, the MSP has earned accolades ranging from Channel Futures MSP 501 to being named SonicWall’s 2024 MSP Growth Partner of the Year. Dan is a true entrepreneur, dedicated to growing, investing in, and mentoring small businesses. You can find him on LinkedIn, where he regularly posts about technology, business, leadership, and community.