Here an issue that we are starting to hear more about for clients in the NJ and NY areas where we are providing IT security / Cybersecurity services and consulting. If fact, we’ve dealt with it internally here at our NJ offices.
The Basics
The Problem
For several years it has been shown that SHA1 is vulnerable and an attacker can exploit that to have his code carry a certificate that appears legitimate. Certificate based authentication is the cornerstone of computing systems security and integrity today. Such exploits can have significant impact such as the 2012 Flame malware. Microsoft plans to deprecate SHA1 certificates by mid-2017.
The Solution
We recommend moving in-house corporate PKI infrastructure to SHA-256 certificates. SHA-256 is a level of SHA2. It’s the most commonly adopted standard at this time (Q1 2017). Higher levels SHA2 such as SHA-512 have been shown to not be supported at this time by major applications such as Internet Explorer, Lync/Skype, …
Challenges and Options
Example of securing IIS server
This PowerShell script automates the process of securing protocols, ciphers, and hashes. This goes beyond the SHA1 issue to disabling weak and vulnerable protocols, hashes, and ciphers that are enabled by default on a Windows computer. This can be run on any computer but is typically run on an IIS server because of its public facing role. The script specifically disables the following legacy protocols, hashes, and ciphers:
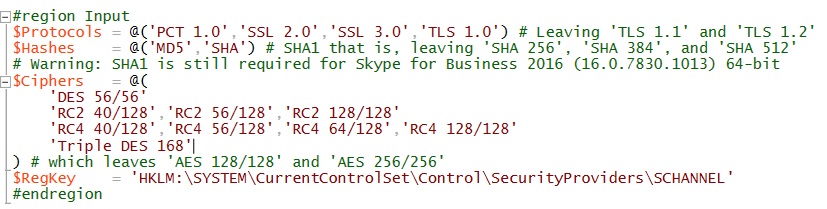
Note that SHA1 is still used by Skype of Business. Disabling SHA (SHA1 that is) hash will cause Skype to fail to sign in.
![]()
Exigent Technologies provides a wide array of IT Security (Cybersecurity) consulting services in the greater NY, NJ Tri-state areas.
For more information on securing your IT infrastructure, contact us.